
The Practitioner's Guide to Risk-Based Vulnerability Management
The implementation playbook for risk-based vulnerability management. Five phases to move from CVSS-sorted patching to a system that prioritises what actually gets exploited.

The implementation playbook for risk-based vulnerability management. Five phases to move from CVSS-sorted patching to a system that prioritises what actually gets exploited.

Patching everything is a losing strategy. Discover why your security team is fixing the wrong vulnerabilities — and what leadership can do about it. A framework for risk-based prioritization that reduces exposure without adding headcount.
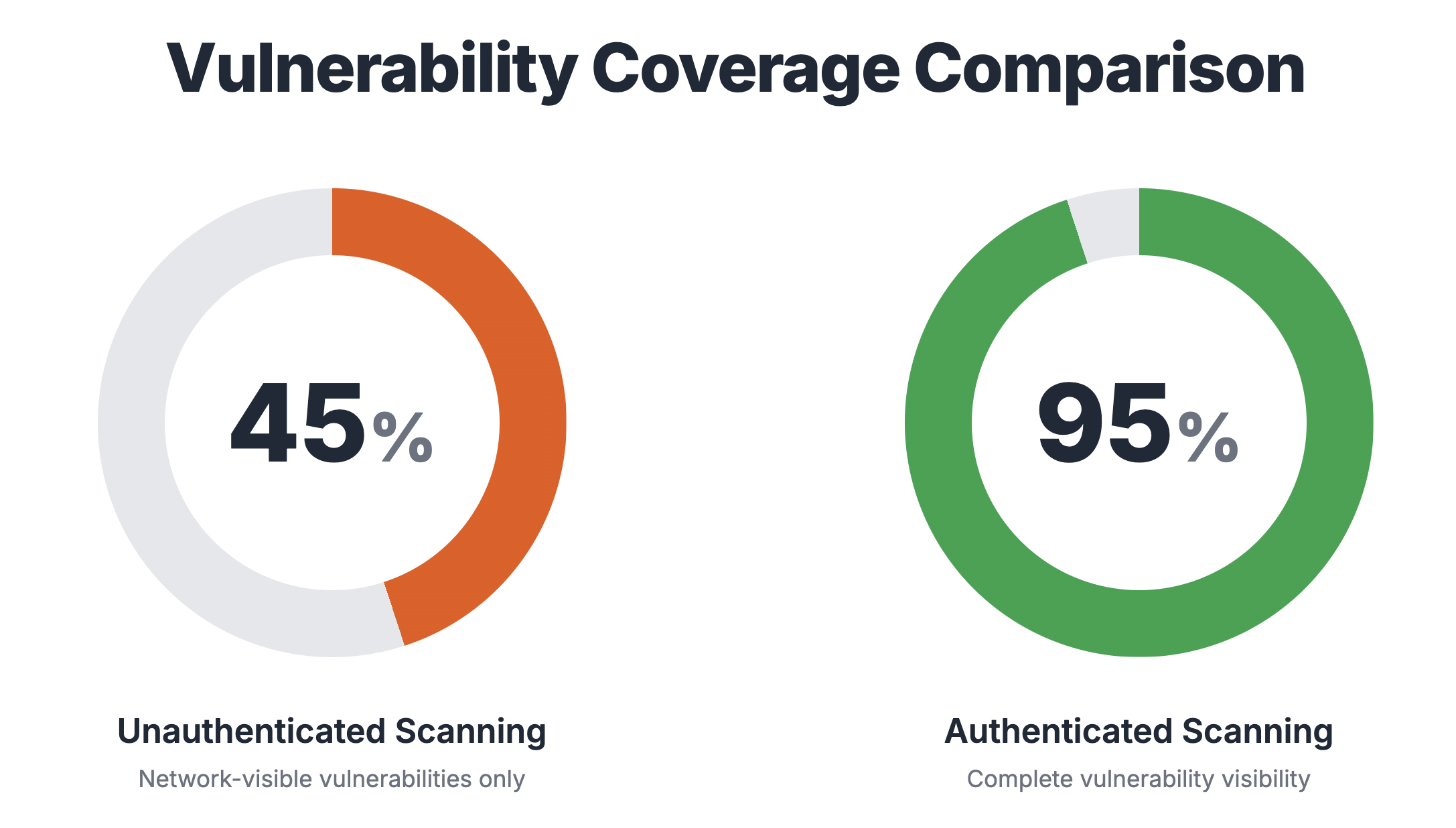
Authenticated scans find 3x more vulnerabilities than unauthenticated scans. See real scan data comparing both methods, plus Log4Shell and PrintNightmare examples showing what you're missing.
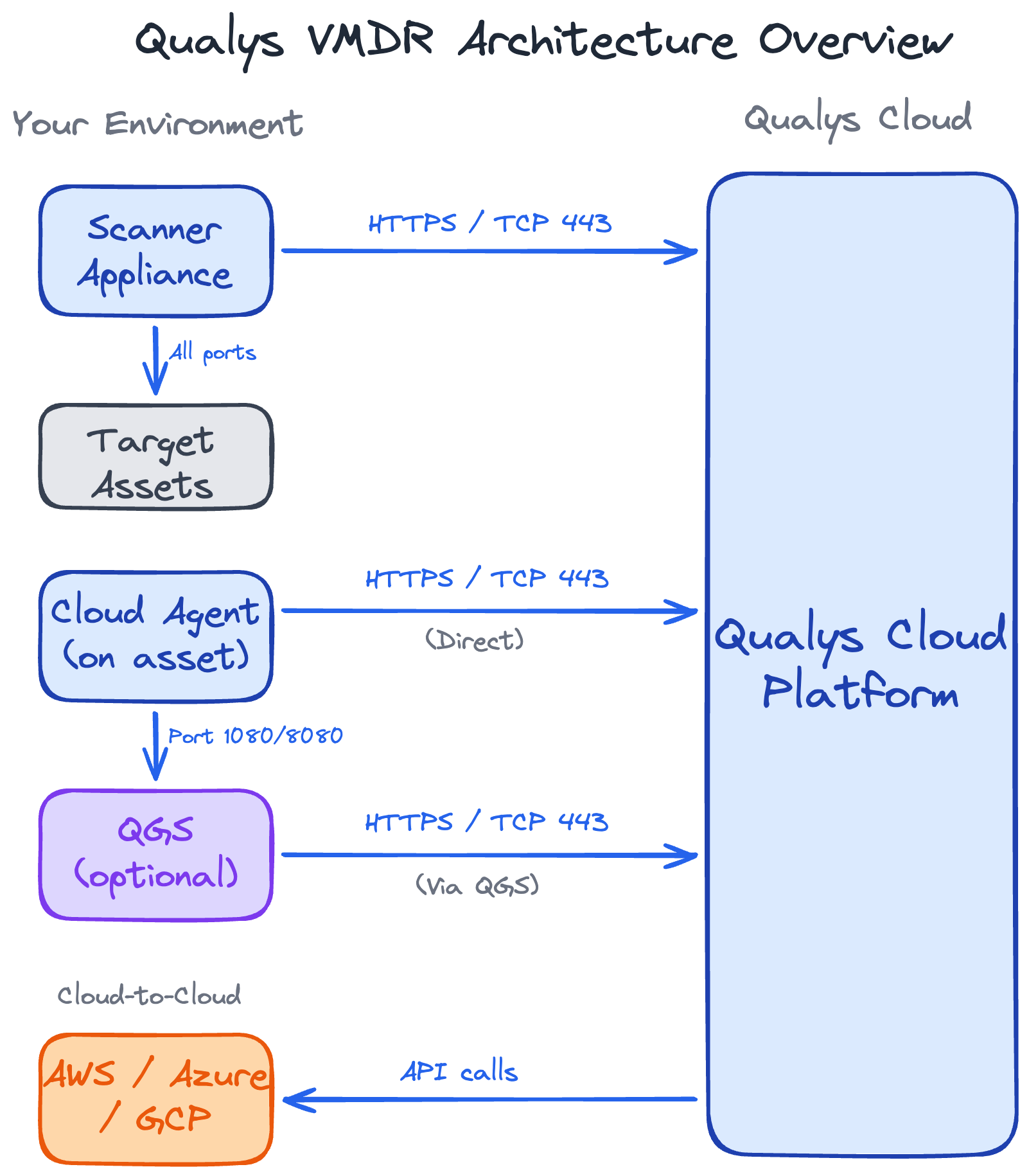
Get Qualys firewall rules right the first time. Complete architecture guide with scanner/agent communication flows, port requirements, firewall rules, and deployment checklists.
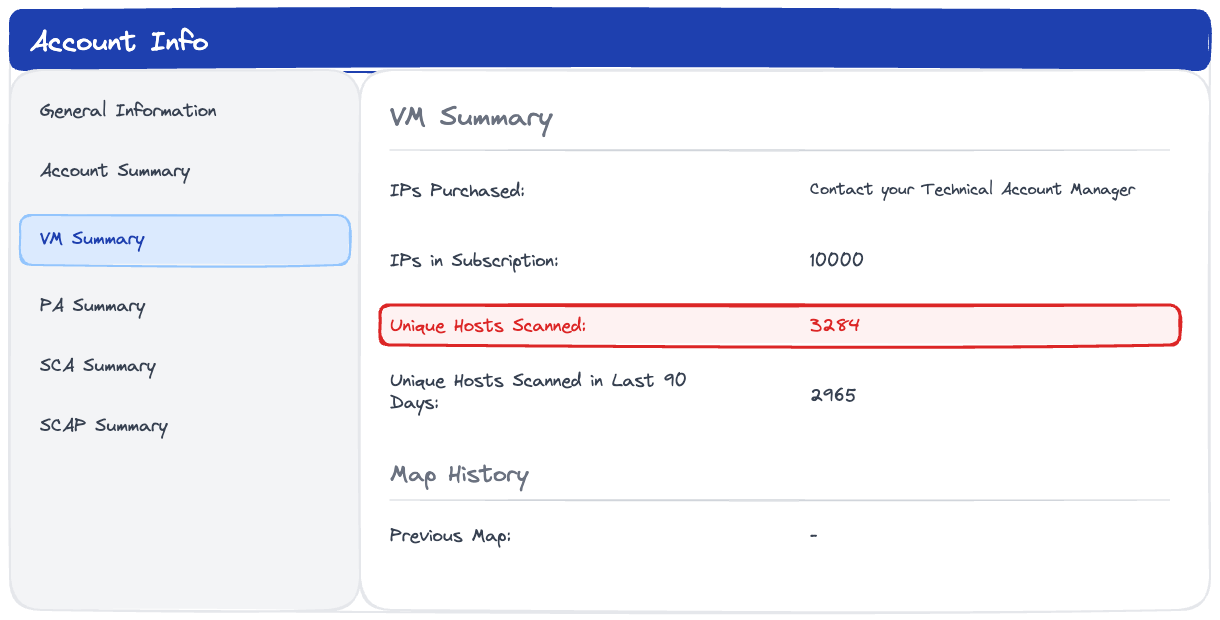
Avoid overpaying for Qualys licenses. Discover how VMDR counts assets, why network devices bloat your license usage, and how to audit your true consumption with API queries.